Security Management

Cloud Security Generation Z
Also known as the 'Cloud Generation,' this Generation Z is already reshaping IT…and careers. Many are...

Forrester Wave, We're a leader!
VMware Carbon Black Named a Leader in The Forrester Wave™: Endpoint Security Software As A Service,...
Aligning Cyber Skills To The MITRE ATTandCK Framework
The MITRE ATTandCK Framework is a comprehensive matrix of tactics and techniques used by threat hunters,...
Cloud Security Automation For Dummies®
Get the big picture on cloud security, in all its complexity, speed, and scale. Our Cloud Security Automation...

Get a Fast Office 365 User Experience
Recommendations for a smooth migration, fast results. A Microsoft Office 365 migration can be daunting....

Rackspace Fanatical Support for AWS
As organizations move their workloads from traditional data centers to AWS, IT security paradigms are...

8x8: Collaboration and AI Take Customer Care to the Next Level
This buyers guide examines the North American contact center market for both premise- and cloud-based...

How to Increase Agility with Hybrid Cloud Automation
As organizations innovate faster than ever, they bring new applications and services to market in more...

BlackBerry Guard: Solution Brief
Many businesses overlook or underinvest in managed detection and response (MDR), a critical aspect of...
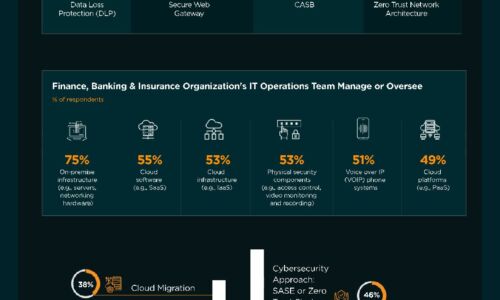
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...
2021 Thales Cloud Security Study
The pandemic has pushed organisations into many changes in the last year but the move to greater use...
Dynamic Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.