Security Management

Insider Threat Prevention Guide
In a perfect world, trust would never be violated. Cyber defenses would be impregnable. No employee would...
Responding Smarter, Faster and Better
In cybersecurity, a critical event is a major incident that's disruptive enough to pose a meaningful...
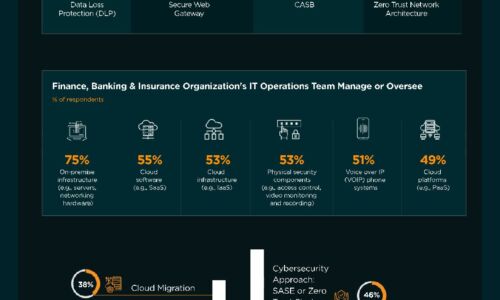
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

The Trouble with Modern Authentication Approaches
Sensitive data is increasingly being accessed by mobile and dispersed workforces from the cloud, resulting...

How to Increase Agility with Hybrid Cloud Automation
As organizations innovate faster than ever, they bring new applications and services to market in more...

Telstra's Best Practice Guide to Hybrid Cloud
Hybrid Cloud is becoming the strategy of choice for enterprises that want the best of both public cloud...
Automation antidotes for the top poisons in cybersecurity management
Cyberthreats are more imminent and dangerous than ever in terms of their persistence and severity. The...

Managing Critical Events with BlackBerry Alert
Every day, organizations face risks from natural, technological, and human-caused critical events. While...

What Today's Retailers Need in a Security Architecture
Retail cybersecurity in the age of the omnichannel customer experience requires CIOs and vice presidents...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.