Email Security
User Risk Report
Your cybersecurity posture is only as strong as its weakest link. And in today's people-centric threat...

7 Ways to Prevent Supply Chain Phishing Attacks
Your email and digital communications with suppliers, partners, vendors and other third parties represent...
2021 State of the Phish
There's no question that organisations (and individuals) faced many challenges in 2020, both new and...

3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...
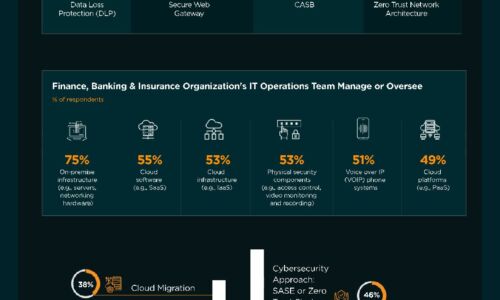
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Use Case-Driven Cloud Security Evaluator Guide
Researching cloud security? Be sure you evaluate yourself and your vendors on the 6 most common cloud...

PhishBusters Survey: Perception vs. Reality of Phishing Attacks
Cofense conducted a survey to examine the general public's perceptions of phishing attacks, including...
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...

Cloud Security Generation Z
Also known as the 'Cloud Generation,' this Generation Z is already reshaping IT…and careers. Many are...

Driving Real Behaviour Change
Today's most potent cyber threat isn't a zero-day vulnerability, new malware or the latest exploit kit....

Rackspace Fanatical Support for AWS
As organizations move their workloads from traditional data centers to AWS, IT security paradigms are...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

