Email Security
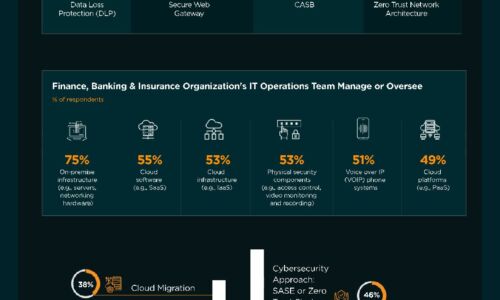
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Python for Data Science For Dummies, 2nd Edition
The fast and easy way to learn Python programming and statistics Python For Data Science For Dummies...

Telstra's Best Practice Guide to Hybrid Cloud
Hybrid Cloud is becoming the strategy of choice for enterprises that want the best of both public cloud...

The Business Email Compromise Handbook
A Six-Step Plan for Stopping Payment Redirection, Supplier Invoicing Fraud and Gift Card Scams Sometimes,...

The Survivor's Guide to Building an Office 365 Network
A Microsoft Office 365 deployment can be daunting. From a fast user experience, to a cost-cutting productivity...
Unmasking BEC and EAC
Whether they result in fraudulent wire transfers, misdirected payments, diverted payrolls, supply-chain...

You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...

Top 3 Challenges Your Team Faces When Building in the Cloud
Today's cloud and security teams are asked to do more with less. Although the capabilities and cost of...
Cyber Risk Commands C-suite's Focus: The State of Email Security 2023
As companies grow more skittish over rising economic volatility and intensifying geopolitical tensions,...

Enable End-to-End Zero Trust To Achieve Effective Outcomes
Zero Trust priorities have evolved in 2020 to require solutions that secure your remote workforce with...

Optimized Security for Multi-Cloud laaS Environments
No question: Multi-cloud adoption can benefit your business. New question: How can you secure multi-cloud...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

