Email Security

Filling the Gaps in Office 365
Office 365 offers a variety of choices and added functionality making it confusing for IT teams to decide...
The Hidden Cost of Free M365 Security Features
All email, cloud, and compliance solutions are not created equal. As organisations make the move to Microsoft...

Email Reporting and Remediation
More than ever, attacks seek to exploit human vulnerabilities, not just technical flaws. In most cases,...

Why you need an adaptive security segmentation solution
The threat landscape is more dynamic than ever before, and as business-critical applications traverse...

Deploying Consistent Application Services in Multi-Cloud Environments
Most organizations prioritize cloud flexibility—and let application teams choose the best environment...
Key Principles and Strategies for Securing the Enterprise Cloud
Customers are turning to the cloud to reduce capital expenses and increase agility as part of their digital...

2022 Annual State of Phishing Report
Enriched with robust threat intelligence from the Cofense Phishing Defense Center (PDC), which analyzes...
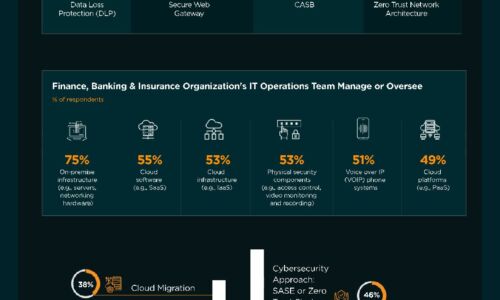
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...

2021 State of Malware Report
The story of 2020 is of the devastating COVID-19 pandemic, and of how the world adapted. The story of...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



