Latest Whitepapers
Embrace Microservices Application Architecture
Today, new application architectures like Devops microservices are opening great opportunities for innovation....

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...

You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...
Secure Beyond Breach
Securing the perimeter is no longer enough. The focus has shifted to ensuring your organization continues...
The Ultimate Guide to Workforce Analytics
Learn how Workday can help your organization understand its employee data to make better people decisions...

Protecting commercial network data in motion
Modern organizations have become dependent upon the fixed, high-speed data networks that serve as their...

4 tips to ensure your board is ready for a successful AGM
The 2022 AGM season is on course to see unprecedented levels of challenge for boards and businesses....
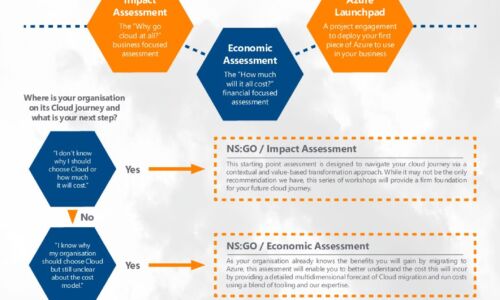
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...

How a Cloud-native CMS Makes Content Delivery Faster and Easier
The world of content management is shifting. Real-time, personalised experiences—like receiving offers...

5 Critical Considerations for DDoS Mitigation
Distributed denial-of-service (DDoS) attacks remain one of the most effective methods used by cybercriminals...

How financial firms build stellar experiences in the cloud
From ordering takeout on an app to joining video calls, the way your customers work and play is constantly...

Top 10 Reasons to Partner with Dell EMC for Windows Server 2016
The release of any Microsoft operating system is always an important crossroads for IT decision-makers,...

Ten Ways Pure’s Flash Solution Can Help You Succeed
Legacy infrastructures are a roadblock to innovation, despite most service providers being heavily reliant...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.






