Software

Leadership trends report: Global app development roadmap 2022-2025
Digital leaders need to keep pace as new technologies are adopted across the enterprise, but today most...
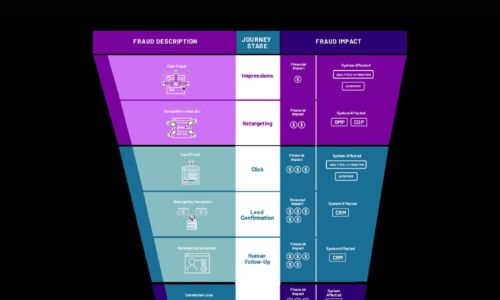
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Best-in-Class SaaS Performance
The average person uses 36 cloud-based services every single day. Now it's up to IT operations teams,...
Overcome Database Indexing Challenges
Overcome your database indexing challenges – read this MSSQLTips white paper today By properly using...
Four Keys to Navigating the Hardware Security Journey
Ensuring enterprise-wide device security requires a shield, or security posture, that follows and protects...

CIO Roadmap to Hybrid and Multi-Cloud
While cloud has become a key driver of business expansion and operational efficiency, business and IT...
The Future of Retail is Conversations
Retail may never be the same. Consumers who were previously averse to online shopping suddenly embraced...

Verizon and Palo Alto Networks Enabling a Secure Connected World
Supporting mobility, minimizing the attack surface, and having reliable access to applications are key...

GigaOm Radar for Phishing Prevention and Detection
Get your complimentary copy of this independent GigaOm Research report, which analyzes positioning and...

2021 Technology Trends IT in Focus
In a world where commercial success is increasingly defined by the quality of the customer experience...

Data Governance Is Everyone’s Business
Erwin's contribution to data governance brings IT and business together for a new era in data-driven...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.