Software
Securing Microsoft 365
Few tools are as critical to modern business as Microsoft 365. Unfortunately, the platform's ubiquity...
Protect and Preserve Your Data from Endpoint to Infrastructure
Technology has made it possible for the world to maintain a somewhat business-as-usual stance, even when...

Why a Backup Strategy for Office 365 is Essential
This short, easy-to-read research paper by IDC provides their view on why having a backup of Office 365...

Forrester Consulting: Bridging The Developer and Security Divide
As security professionals work to create a secure environment for organizations, developers are often...

Top 4 Pitfalls to Avoid when Deploying Office 365
There's no denying that Office 365 is a big deal. It's a big part of the Microsoft Intelligent Cloud...

Getting started with SASE:
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...
Why dirty data can stop quote-to-cash processes in their tracks
It's been 15 years since mathematician Clive Humby uttered those famous words: 'Data is the new oil....

Developing a data mindset
Change your mindset to change your organization. Leaders know the importance of data. The challenge is...
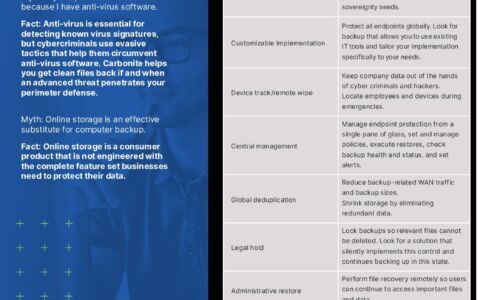
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Human Potential: Unlocked
Find solutions to the problems that matter to you, the CHRO. Managing risk, increasing revenue, boosting...

Harden your attack surface with workflows and automation
Remote work and the acceleration of digital transformation during the COVID-19 pandemic has pushed more...

2020 IT Skills and Salary Report
The COVID-19 pandemic has placed greater emphasis on the need for skilled IT and tech professionals to...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

