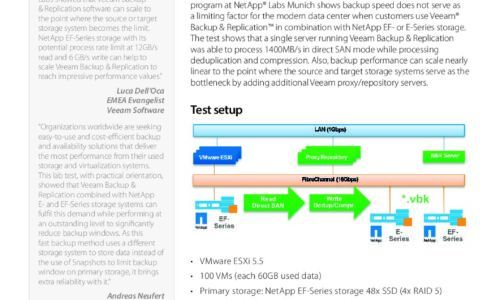
Backups

12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...

5 Remote Work Threats and How to Protect Against Them
With the surge in remote work, many IT and security teams are forced to make security tradeoffs to maintain...
Defend Against Ransomware
Defend your organization from evolving ransomware attacks. Learn what it takes to reduce risk and strengthen...

Data Management in a Multi-Cloud World: Finance and Insurance Edition
This report focuses on a recent quantitative research study conducted with UK and Ireland IT decision...
User Risk Report
Your cybersecurity posture is only as strong as its weakest link. And in today's people-centric threat...

Learning SQL: Generate, Manipulate, and Retrieve Data
As data floods into your company, you need to put it to work right away—and SQL is the best tool for...
How 3 Leading Organizations Took the Fast Path to Cloud
VMware Cloud on AWS Case Studies. Whether you are faced with moving specific applications to the cloud,...

VMware Cloud Workload Migration Tools
Before starting a cloud migration project, it is critical to understand the strategies and tools available...

Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.