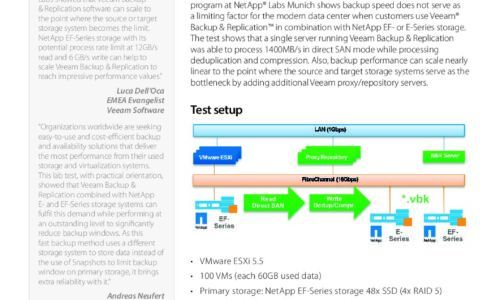
Backups

Using data to empower your transformation
Harness the power of data. To be a leader that's going to reinvent, you have to be relentless and tenacious...

Learning SQL: Generate, Manipulate, and Retrieve Data
As data floods into your company, you need to put it to work right away—and SQL is the best tool for...

12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...

Overcoming the Top Five Gaps in Office 365 Data Protection
Microsoft Office 365 is widely used. Whilst it does offer a variety of system availability and data protection...

7 Critical Reasons for Office 365 Backup
You have one more reason added to the 6 critical reasons to protect your Office 365 data. This 5-minute...

2022 MSP Threat Report
This report was created by the ConnectWise Cyber Research Unit (CRU)—a dedicated team of ConnectWise...
A Guide for SMBs: Can I really become 'less hackable'?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...
Learn how to build a business framework designed for data management
The center of a best practice approach must include a complete view into your organization and its technology...

2022 Threat Report
The BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a...

Unified Fast File and Object (UFFO) Storage
In this book, you get an idea of the vast potential for unstructured data — and also the infrastructure...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.