Latest Whitepapers
Linux Bible, 10th Edition
Linux Bible, 10th Edition is the ultimate hands-on Linux user guide, whether you're a true beginner or...
Merger and Acquisition IT Integration: Active Directory
Each IT integration project is unique based on the timelines, the makeup of the environment and the goals...

Data Management in a Multicloud World – Finance and Insurance Edition
This report focuses on a recent quantitative research study conducted with UK and Ireland IT decision...

An Expert Guide to SQL Server Performance Tuning
Database professionals agree – SQL Server performance tuning is challenging. And, as with many daunting...

Preparing Your Remote Work Environment for the Long Haul
Enabling users to work from anywhere has been a core benefit of desktop and app virtualization from the...
Report: Forrester TEI for CSM
To deliver effortless, end-to-end customer experience every time, all parts of your organisation need...
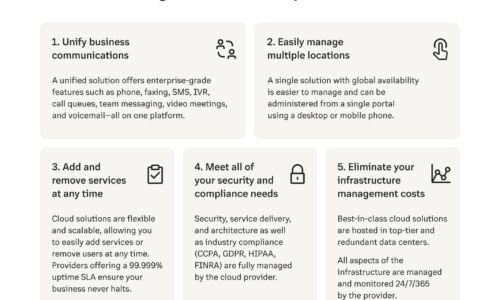
7 Reasons to Switch your On-Premises PBX to the Cloud
Businesses going remote or hybrid require more than what an on-premises PBX can provide. With a cloud...
Why dirty data can stop quote-to-cash processes in their tracks
It's been 15 years since mathematician Clive Humby uttered those famous words: 'Data is the new oil....

Getting Faster: Know Your Website, and Know What's Slowing It Down
Speed and performance of your website significantly impact revenue growth and conversions. The numbers...

Choose the WAF That’s Right for You
Despite the industry's best efforts to bolster secure application development practices, the growing...
Protect and Preserve Your Data from Endpoint to Infrastructure
Technology has made it possible for the world to maintain a somewhat business-as-usual stance, even when...

Dell Latitude Rugged PCs
Get best-in-class reliability and productivity in the harsh conditions you face with the Dell Latitude...

How to Ensure your Digital Experience Platform is Right for your Needs
Customers' expectations have never been higher. We all expect more, especially online. We want experiences...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.






