Latest Whitepapers

Digital Transformation – It’s in the Way You Move IT
As enterprises consider a migration to the cloud, many are left wondering: How can we ensure success? Download...
5 Signs MDR Is Right for Your Organization
Perhaps you've been considering a managed detection and response (MDR) solution, but you aren't quite...

Challenging Times Call for a Cybersecurity Plan of Action
Could there be a more 'exciting' time to be a cybersecurity executive? Some might choose other adjectives:...
A Planning Guide for Media Organizations
As the world continues to change, media organizations that want to stay ahead must quickly learn how...

Moving Endpoint Security to the Predictive Cloud
Traditional antivirus (AV) vendors aren't keeping up with today's threats. They don't protect against...
Moving Forward in a Work-from- Anywhere World
Welcome to The Gorilla Guide To…® Moving Forward in a Work-from-Anywhere World, Foundation Edition....

CMO's Guide to AI for Customer-Centric Marketing
AI allows marketing leaders and their teams to quickly analyze vast amounts of customer data to predict...

Book of Knowledge for Customer Experience
Technology is always evolving, and customer expectations are evolving with it. ServiceNow is helping...

Digital Transformation: Are We Finally Past the Unmet Expectations?
Digital transformation is no longer a mystery to enterprises, but they still have many questions. What's...

AI-Driven Threat and Incident Prevention, Detection, and Response
Traditional cybersecurity, for lack of a better word, is dead. The proliferation of mobile technology...

A Fresh Look at Online Food Delivery and Grocery Trends
The world is experiencing a digital shift, with everyday chores and activities being completed with the...
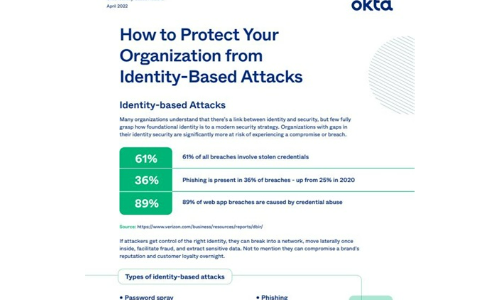
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.