Storage
The CIO's Guide to Cloud Data Management
Data is power. How you use it and how you protect it is critical. As a CIO, you are responsible for leading...

Veeam Enterprise Availability for SAP HANA
Enterprise-grade companies uses SAP HANA worldwide, this is the application directly related to customers...

OptiPlex: The Desktop Re-imagined
For 25 years, OptiPlex has continuously adapted to the new ways you work. The next generation of innovative...
Evolution Of The Marketer's Toolkit
More than ever, enterprise organisations need a 360-degree view of their customers to deliver the kind...

Dell Latitude Rugged PCs
Get best-in-class reliability and productivity in the harsh conditions you face with the Dell Latitude...

Cyber Attack Trends: Check Point’s 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...

Fortinet Security Solutions for SAP S/4HANA
With today's challenges and economic climate, organizations leverage enterprise resource planning (ERP)...

Leadership trends report: operating excellence
Optimising business operations used to mean just lowering costs and increasing profits. But today, you...
One secure platform for banking and capital markets
Easy, secure client experiences are the new gold standard in financial services. Whether you're talking...

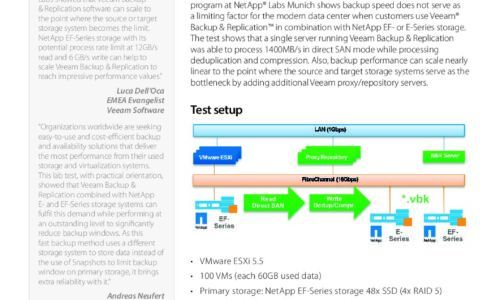
The Impact of Accelerating Storage and Data Protection Environment
ESG recently surveyed 2,000 IT decision makers to understand whether, and to what degree, organizations'...

SD-WAN in the Age of Digital Innovation
Achieving Business Agility While Reducing Disruption. Most organisations are in the midst of some form...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.