Storage Management

Transform Your Field Service with a Great Customer Experience
Full Offline Working, Flexible Architecture, Reusable Components Faced with pressures from both the business...

GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Tintri Introduces SQL Integrated Storage
What is SQL Integrated Storage? A SQL database is, essentially, a collection of files with associated...
The Role of Machine Learning and Automation in Storage
There has been lots of hype around the increasing role that machine learning, and artificial intelligence...
The Business Value of Storage Solutions from Dell Technologies
In the era of digital transformation — the evolution toward much more data-centric business models...

Unlocking collaboration in higher education
Collaboration and knowledge sharing are pillars of higher education. Instead of working in silos detached...

Enterprise Cloud Solutions
Many traditional infrastructure vendors would have you believe that hyperconverged infrastructure is...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...

A New Sequence for Bioinformatics HPC
Dell Technologies and AMD The UK National Health Service is collaborating with university partners to...

Pure Storage FlashBlade: Unified Fast File and Object (UFFO) Platform
Operational efficiency is the most-cited objective for digital transformation according to ESG research....

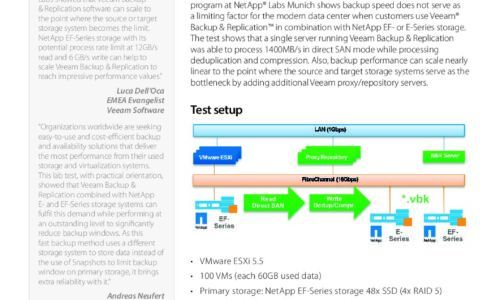
The Gorilla Guide to Rapid Restores with Flash and Cloud
Welcome to this Gorilla Guide covering enterprise data protection, backup, and recovery. The purpose...

All-Flash Buyer's Guide: Tips For Evaluating Solid State Arrays
Are you looking to switch to all-flash storage? Learn how to evaluate your storage options to increase...

Building Modern Data Architectures
As the amount of data multiplies, the challenges of managing this data have multiplied, too. Data now...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.