Software

CIO Insights on Accelerating Finance Transformation
Learn how IT leaders can help finance teams achieve their goals and accelerate digital transformation...

The State of Application Development: Is IT Ready for Disruption?
Organizational agility is more important today than ever. Digital transformation has dominated business...

Securing financial services network data
Financial services is one of the most tightly regulated business sectors. The FSA, the Data Protection...
Achieving Zero Trust with Illumio
Enterprises struggling with increasingly complex infrastructure are turning to Zero Trust as a common...

Efficacy Of Micro-Segmentation Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....

Forrester Wave Report
In our 33-criteria evaluation of web application firewall (WAF) vendors, we identified the 10 most significant...

Learn the 10 questions your cloud partners should be able to answer
Evaluating cloud partners can be overwhelming. These 10 key questions will help find who's best suited...

Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

2021 State of Data Governance and Empowerment
Organizations are embracing their data-centric futures. They are making more data available to more people...

Cloud Adoption Essentials Guide
Organizations have been moving more and more workloads to the cloud for some time, but this trend is...
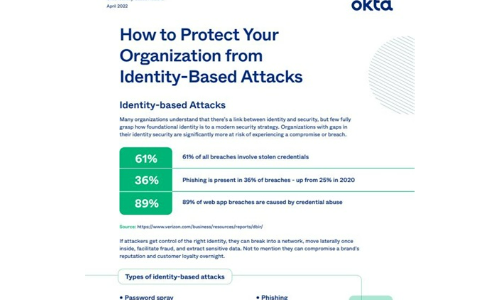
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


