Server
NoSQL for Dummies
This easy to read guide to NoSQL databases provides the type of no–nonsense overview and analysis that...

Ransomware Defense for Multi-Site Enterprises: How to Recover Faster
Ransomware is evolving, forcing enterprises to change how they prepare for attacks. While the focus on...

Improving Threat Hunting with Big Data
A recent survey of IR professionals1 indicated that while financial and retail sectors are the most targeted...

Accelerating Your AWS Journey
Migrate and modernize to accelerate operational efficiency. Get the speed and agility you need to delight...

Assessing Network Traffic Analysis (NTA) Requirements
Many organizations are struggling to detect, hunt, investigate, and respond to threats in an efficient...
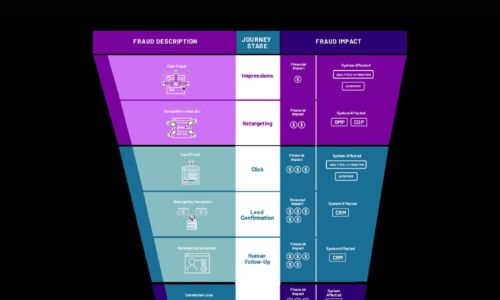
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Sophos 2022 Threat Report
Interrelated threats target an interdependent world. We believe that shifting the timescale of attack...
Succeeding With Analytics in the Cloud
Enterprises today recognize that cloud is integral to their digital transformation. As organizations...
Cloud Workload Protection
The hybrid cloud is at the centerpiece of digital transformation. Today, more than 90 percent of enterprises...

Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



