Server

Hybrid Work: Why it's time to move your on-premises PBX to the cloud
For years, the shift to cloud-based communications services was gradual, with some organizations going...

Enterprise Cloud Solutions
Many traditional infrastructure vendors would have you believe that hyperconverged infrastructure is...

Efficacy of Micro-Segmentation: Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....

Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...
5 Steps to Improving Knowledge Management
Advania is an official partner for 4Industry, the digital knowledge management platform for the manufacturing...

Pure Storage FlashBlade: Unified Fast File and Object (UFFO) Platform
Operational efficiency is the most-cited objective for digital transformation according to ESG research....

Forrester Wave Report
In our 33-criteria evaluation of web application firewall (WAF) vendors, we identified the 10 most significant...
The Pitfalls of SASE Vendor Selection: Features vs. Strategic Outcomes
After speaking with 1000s of IT pros, we've learned that success with SASE is only achieved when it meets...
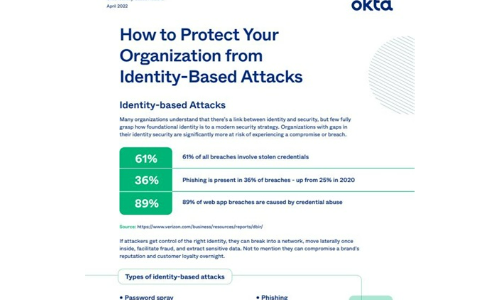
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Spotlight: The State of SMB and IT Today
The small and midsized businesses (SMB) continue to be powered by the entrepreneurs who want to build...

Data In, Value Out
In today's increasingly data-driven business landscape, the companies who succeed are typically those...
Container Security 101: Understanding the basics of securing containers
Containers are quickly becoming an essential part of many IT development environments, but their popularity...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.