Security Solutions

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...

Artificial Intelligence: The Smarter Approach To Information Security
The news headlines are replete with stories of devastating data breaches, compromising the personal and...

Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your teams with...

Spear Phishing: Top Threats and Trends
Cybercriminals are constantly refining their tactics and making their attacks more complicated and difficult...
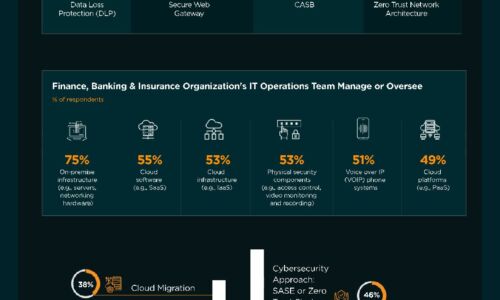
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Solve the security puzzle with end-to-end security solutions
As an IT decision maker, you're focused on finding effective solutions you can implement quickly and...

Guide to Strengthening Mainframe Security
Successful phishing attacks lead to a loss of control over user IDs, passwords and credentials. Bad actors...

5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.





