SAN
Enterprise-Wide Network Segmentation
The promise of digital transformation efficiencies, innovation and productivity has resulted in flat,...

Power Up Your Black Friday
This ebook is part of our Mastering Black Friday series — designed to help your marketing team better...
Report: ICS/OT Cybersecurity 2021 Year in Review
Dragos is excited to present the fifth year of the annual Dragos Year In Review report on Industrial...

2021 Digital Trends Media, Entertainment and Telecoms Industry
The 2021 Digital Trends Report looks to both the past and the future, presenting two equally valuable...

Marketing and IT: The Digital Transformation Dream Team
Brands need to take more control over how they engage customers. To make this happen, Marketing and IT...

The Difference Between API Gateways and Service Mesh
In this eBook, Kong Inc Co-Founder and CTO Marco Palladino illustrates the differences between API gateways...
The Total Economic Impact™ Of Red Hat OpenShift Cloud Services
Modern-day companies are expected to have the capabilities, skills, and tools to support evolving customer...
An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...

Top Ways FinTech Aggregators are Impacting FinServ in 2022
Emerging financial services and banking digital ecosystems are rapidly changing how different organisations...
Digital Transformation: A Look Ahead
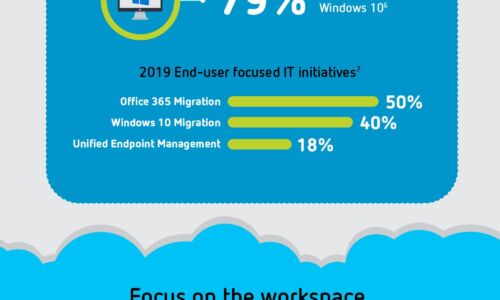
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...
Moving Forward in a Work-from- Anywhere World
Welcome to The Gorilla Guide To…® Moving Forward in a Work-from-Anywhere World, Foundation Edition....

Seamless and Simple Migration to the Cloud
Applications are the heart of every modern organization. As digital transformation becomes increasingly...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

