Network
How to Tackle Ransomware by Managing Human Risk
CybSafe's analysis of ICO data finds the number of incidents of ransomware reported has doubled in a...

Everyone’s talking customer experience. Let’s make it happen.
The health of your brand, products, and services depends on delivering exceptional experiences time and...

Start your data modernization journey
Take the complexity out of your data infrastructure. For organizations running legacy data infrastructure...

The AI & Machine Learning Imperative
Companies across various industries are seeking to integrate AI & machine learning (ML) into workflows...
Implementing Zero Trust Best Practices
Network security challenges have evolved significantly over the years as users have become increasingly...

5 Best Practices for CISOs Adopting XDR
The pace of change in IT infrastructures is unyielding. With XDR, cybersecurity teams can keep up, improve...
The Data Breach is Coming from Inside the House
Real-Life Tales of Data Loss, Insider Threats and User Compromise Data doesn't lose itself. People lose...
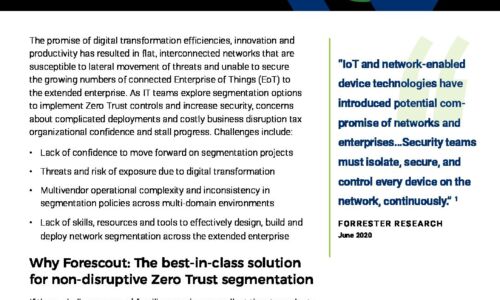
Enterprise-Wide Network Segmentation
The promise of digital transformation efficiencies, innovation and productivity has resulted in flat,...

Not All End User Experience Monitoring Solutions Are Created Equal
Digitization has undoubtedly changed the way companies do business with their customers, partners and...

The Enterprise Guide to Migrating to the Cloud
Enterprises worldwide are competing to develop the most innovative and reliable applications to meet...

Dissecting a Cloud Attack: Securing Azure with AzLog
Microsoft Azure is one of the fastest-growing cloud infrastructure services. Unfortunately, the advantages...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


