Network
Cloud Cyber Resilience Report
After a dynamic year for cloud native apps, Tenable has compiled a report focusing on trends and recommendations...

Case Study - AXA Sigorta
The insurance industry is rapidly becoming a digital experience and insurance providers are racing to...

Shift your Web Security to the Cloud, for the Cloud
As enterprises embrace digital transformation, the adoption of software-as-a-service (SaaS) is robust...

Block by Block: Building for an App-Centric Future
Dell Technologies and AMD The future is being written inside applications. This is where consumer demands...
Become (and remain) the disruptor
If you thought digital disruption was a one-off process to be completed (or resisted), unlocking a new,...
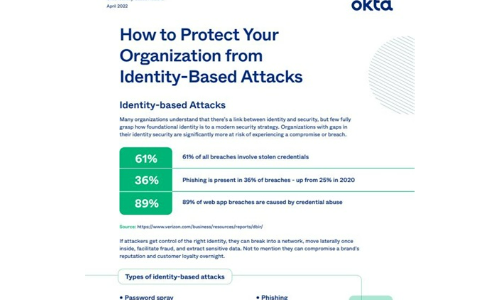
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

A Fresh Look at Online Food Delivery and Grocery Trends
The world is experiencing a digital shift, with everyday chores and activities being completed with the...

Business Value of Cloud Modernization
Explore the business value of proven modernization paths Understanding the business value of infrastructure...

Cloud networks: Shifting into Hyperdrive
Public cloud is driving digital innovation. As IT organizations around the world continue to radically...

Zscaler Private Access as an Alternative to VPN
For almost 30 years, enterprises have relied on the remote access VPN to connect remote users to the...

Seven Multi-Cloud Success Stories
Worldwide Organizations are Transforming IT—and their Business—with VMware Cloud Technologies Now...
Four Keys to Navigating the Hardware Security Journey
Ensuring enterprise-wide device security requires a shield, or security posture, that follows and protects...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
