IT Threats & Vulnerabilities

3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...

The Case for Secure Communications
The tapping of voice communications has occurred virtually as long as electronic communication has been...

Chart Industries vaporizes ransomware and malware
Malwarebytes enables IT to shift its focus to strategic security project work. The company in this case...

How Malware Can Steal Your Data
As applications drive business, more and more valuable data is accessed and exchanged through them. Cybercriminals...

Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...
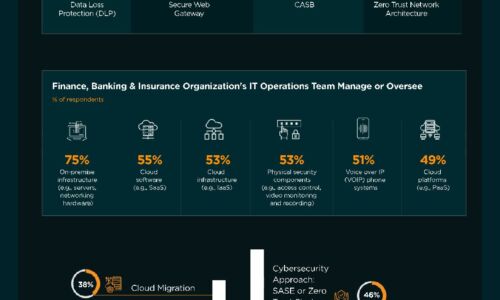
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

The Future of Secure Communications
How BlackBerry's SecuSUITE is changing the way governments and enterprises communicate. In an increasingly...

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...

Securing Cloud Transformation with a Zero Trust Approach
When it comes to rates of change, cybersecurity has rightly been on the conservative side. Setting up...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



