IT Security

Dissecting a Cloud Attack: Securing Azure with AzLog
Microsoft Azure is one of the fastest-growing cloud infrastructure services. Unfortunately, the advantages...
Ransomware Protection with Pure Storage® and Commvault
Ransomware attacks continue to be top of mind for business and IT leaders. And for good reason. They...
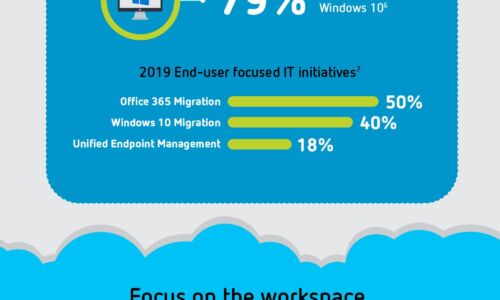
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

The Total Economic Impact™ Of Dell EMC Servers For SAP
To run a digital business that is Intelligent and agile, your enterprise requires an IT landscape capable...

Cloud Security Generation Z
Also known as the 'Cloud Generation,' this Generation Z is already reshaping IT…and careers. Many are...

Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...
Learn how to build a business framework designed for data management
The center of a best practice approach must include a complete view into your organization and its technology...

The VMware Guide to Disaster Recovery Readiness
When it comes to data, planning for the unexpected is of paramount importance—especially today. But...

Nasuni–Smart Storage Strategies for Ransomware Mitigation and Recovery
With the presumption that ransomware will strike their organization at some point, IT leaders must implement...

Ponemon Report
Ponemon surveyed 1,826 IT professionals globally to understand the state of SD-WAN, SASE and Zero Trust...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


