IT Security
Transforming the SOC: Building Tomorrow’s Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Digital Transformation: A Look Ahead
Digital transformation is reshaping organizations into digital businesses. Organizations are focused...

2021 Voice Of The CISO Report
There's no question that 2020 was a challenging year. The pandemic placed an enormous strain on the global...

Rebellions and rejections report
The global pandemic forced organizations to pivot rapidly from an office-based workforce model to one...

5 Critical Requirements for Internal Firewalling in the Data Center
Preventing hackers from hiding inside large volumes of east-west network traffic has now become critical...

Using the Azure Ecosystem to Get More from Your Oracle Data
How much more value and intelligence could you get from your Oracle data if you could work with it in...

Protect your Data and Secure your SQL Server Database Operations
You manage hundreds of SQL Server databases spread over multiple sites and departments, even as you face...

Cybersecurity for retail: Prevention is better than the cure
Prevention is almost always better than the cure. But how many organisations are living up to the promise...

State of Ransomware Readiness Report
2021 has been the year of ransomware. Overall, 80% of businesses around the world have been attacked...

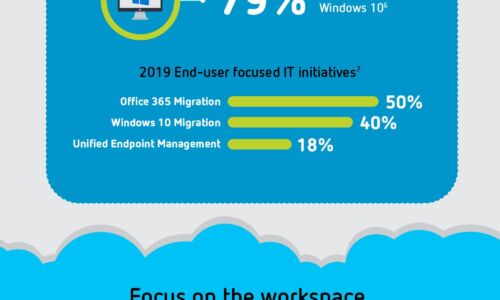
Mitigating Information Security Risks in Microsoft 365
Microsoft 365 offers multiple tiers of capabilities that all leverage the cloud to enable professionals...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.