Firewall
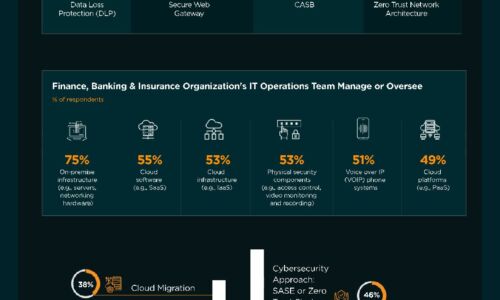
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Reinventing work
We're coming off one of the most challenging years in business history. The pandemic forced every company...

Cloud-delivered security for the digital workspace
With the adoption of hybrid cloud and the rise in remote work, traditional connectivity models like VPN...

5 Things You Didn’t Know About DDoS Attacks That Can Cost You
To accurately determine your organization's risk of a DDoS attack, you must be aware of the latest trends...

Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...

Threats to DNS Are Threats to Your Business. What You Can Do
DNS is a foundational part of the internet, and its hierarchal structure is well known and understood....

Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

Securing high tech industry network data
We all understand the negative impact of data loss, so why is it that so many organisations seem to be...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.