Firewall

The Mimecast-Netskope-CrowdStrike Triple Play
Security and IT organizations must protect against new attacks at scale — and safeguard data in use,...

Oracle NetSuite Protects Flagship Business Applications With Illumio
Find out how SaaS leader Oracle NetSuite improves security and uptime for 7,500 application workloads...
Enterprise-Wide Network Segmentation
The promise of digital transformation efficiencies, innovation and productivity has resulted in flat,...
Definitive Guide to SOAR
How to stop threats faster with security orchestration, automation, and response. Cybersecurity organizations...

Security Starts Here: Privileged Access Management
The threat of a security incident or critical error is very real, and it's something that auditors are...
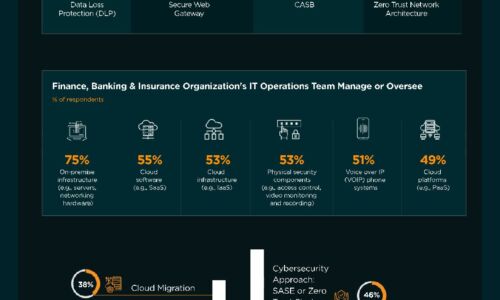
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Farewell ISDN. Hello All-IP.
Analogue and ISDN telephony is a thing of the past – telephony today is mostly internet-based. Voice-over-IP...

Cybersecurity For Dummies
Advanced threats have changed the world of enterprise security and how organizations are attacked. These...

Future-Ready Identity and Access Management
This e-book offers five fundamentals to help you find a new approach to identity access and management...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



