ERP
Using MITRE ATTandCK™ in Threat Hunting and Detection
MITRE ATTandCK ™ is an open framework and knowledge base of adversary tactics and techniques based...
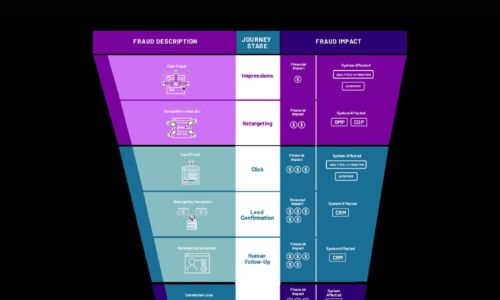
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Cloud-delivered security for the digital workspace
With the adoption of hybrid cloud and the rise in remote work, traditional connectivity models like VPN...

G2 community reviews ServiceNow App Engine
It's clear that rapidly building custom apps is vital for creating and taking opportunities for growth....

The Impact of Accelerating Storage and Data Protection Environment
ESG recently surveyed 2,000 IT decision makers to understand whether, and to what degree, organizations'...
Explore your SASE side
Secure Access Service Edge (SASE), is an architecture that ultimately will integrate networking and network...
SASE & ZTNA for Dummies
SASE and ZTNA combine SD-WAN efficiencies with a flexible, user-centric approach to securing remote workers...

Making the Right Move: Databases in the Cloud
For database managers and users, moving to the cloud means breaking through the confines imposed by capacity...

Manage less. Build Faster. Innovate more.
Learn why AWS is the best place to build modern apps Through our experience building applications for...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.