Endpoint Security

Blurred Lines and Blind Spots Report
Of the many effects the COVID-19 pandemic has had on business, one of the most dramatic has been the...

Accelerating Digital Transformation through Hyper-Converged Solutions
How can organizations simplify IT in order to improve business agility, enhance financial return on investment,...
Fortinet Federal Government Cybersecurity Solutions
U.S. federal agencies operate some of the world's largest and most complex digital networks, but many...
Hidden Costs of Endpoint Security
When it comes to endpoint security, CISOs are in a bind. Most assume that endpoints will be compromised...
A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...
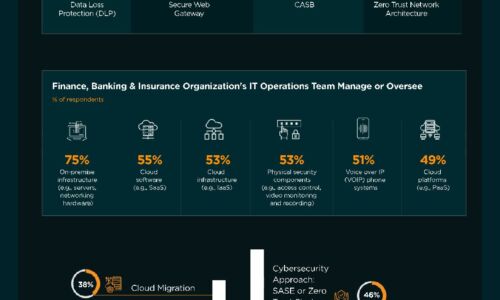
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Aruba Edge-To-Cloud Security
Growth at the edge in the form of remote users and large numbers of new IoT devices has created unique...

10 Endpoint Security Problems Solved By The Cloud
Are you experiencing problems with your traditional AV solution? Read the eBook 10 Endpoint Security...

The SMB Opportunity for MSPs: 2021-2026
According to new research from ConnectWise, MSP industry trends show that SMBs will create over $90 billion...

Seven Strategies to Securely Enable Remote Workers
Is your organisation ready to securely support a wide range of remote workers in the wake of a global...
5 Uncomfortable Truths About Phishing Defense
When over 90% of breaches start as phishing emails threats that email gateways miss and other defenses...

Consolidate Cybersecurity Vendors to Accelerate Detection and Response
Organizations of all shapes and sizes are increasingly embracing digital transformation, cloud-delivered...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

