Introducing the Sotero Data Security Platform
IT security professionals continue to struggle with managing countless security solutions and disparate...
MIT Executive Guide: The AI and Machine Learning Imperative
Companies across various industries are seeking to integrate AI and machine learning (ML) into workflows...

How 5 Enterprises Consolidated ITSM to Reduce Costs
See how five leading brands modernized ITSM with ServiceNow. For businesses that want to transform, modernizing...
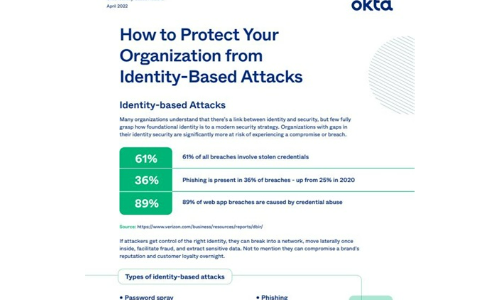
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

How Proofpoint EFD Is More Than Just DMARC
A raft of solutions have sprung up to help organisations set up and manage their DMARC strategies. Like...
From Seismic Disruption to a New Era of Success
No one could have foreseen the terrible impact of the COVID-19 outbreak on humankind. In business too,...

Unified Communications as a Service
As businesses increasingly embrace a cloud-first strategy, many are migrating their most heavily used...

DDos is the New Spam: 3 Strategies to Turn Catastrophe into Annoyance
As DDoS attacks grow larger, more complex, and more pervasive, it can feel like we face a future of inevitable...
Achieve Cloud Security Cost Savings Through SIEM Optimization
Tame Rising SIEM Costs and Complexity Do you worry that your SIEM is falling behind on efficiently handling...

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...

Protection From the Perfect Storm
Connectedness is defining our lives as never before. With Internet-enabled IoT devices multiplying exponentially...

2022 Voice of the CISO
Though less eventful than its predecessor, 2021 was another blockbuster year for cybersecurity. With...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

