Data Recovery
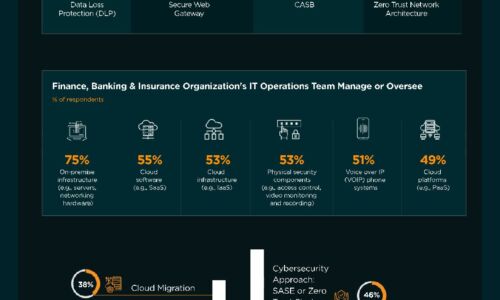
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

Securing Privileged Accounts: Three Steps to Maximize Protection with MFA
Hackers are eyeing your privileged accounts, so you better be using more than 'admin123' to secure them. Multi-factor...

Protect your Data and Secure your SQL Server Database Operations
You manage hundreds of SQL Server databases spread over multiple sites and departments, even as you face...
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...

Learn the 10 questions your cloud partners should be able to answer
Evaluating cloud partners can be overwhelming. These 10 key questions will help find who's best suited...

Cloud Security Generation Z
Also known as the 'Cloud Generation,' this Generation Z is already reshaping IT…and careers. Many are...

You've Got BEC!
A Roundup of the 10 Biggest, Boldest, and Most Brazen Business Email Compromise Scams of 2020 and 2019. It's...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...

Cybersecurity Insiders: Cloud Security Report
The 2019 Cloud Security Report from Cybersecurity Insiders highlights what is and what is not working...

10 Ways to Fortify Ransomware Recovery Defenses
Ransomware has become a 'cyber-pandemic' that shows no signs of diminishing anytime soon. Your ransomware...
Combatting Ransomware by Exposing the Myths
Ransomware continues to pose a credible and costly threat to the enterprise. Misinformation only compounds...

Decoupling security from the network: The evolution of segmentation
You rely on the network to deliver applications. But as IT scales in size, connectivity, and environments...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
