Data Loss Prevention (DLP)
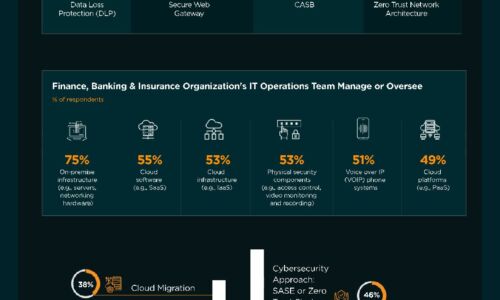
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

Optimized Security for Multi-Cloud laaS Environments
No question: Multi-cloud adoption can benefit your business. New question: How can you secure multi-cloud...

Moving Endpoint Security to Predictive Cloud
Endpoint security is broken. Traditional antivirus (AV) vendors aren't keeping up with today's threats....

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...

Why you need an adaptive security segmentation solution
The threat landscape is more dynamic than ever before, and as business-critical applications traverse...

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Transforming Security in the Mobile Cloud Era
In the age of digital transformation, maintaining secure interactions among users, applications, and...

The Case for Secure Communications
The tapping of voice communications has occurred virtually as long as electronic communication has been...

Get a Fast Office 365 User Experience
Recommendations for a smooth migration, fast results. A Microsoft Office 365 migration can be daunting....

Securing Privileged Accounts: Three Steps to Maximize Protection with MFA
Hackers are eyeing your privileged accounts, so you better be using more than 'admin123' to secure them. Multi-factor...

Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...

Advanced Email Security
Email is a fundamental feature of modern business. Yet it is also the number one threat vector. Email...

Cybersecurity Insiders: Cloud Security Report
The 2019 Cloud Security Report from Cybersecurity Insiders highlights what is and what is not working...

A Guide To Implementing a Secure SAP System with Fortinet
With today's rapidly changing market conditions and economic climate, organizations are using enterprise...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.