Compliance

Public Sector Cloud Journey
As the government continues to move workloads to the cloud, many agencies are struggling to automate...

The evolution of process automation
Automation has a long and storied history. Today, advancements in artificial intelligence (AI) are spawning...

Top Ways Your Cloud Approach is Burning Cash
Through our work across hundreds of clouds and tens of thousands of containers and workloads, we've captured...

DEVSECOPS: Staying Secured and Compliant in a High Paced Release Cycle
The rapid adoption of cloud technology and evolution of the software industry from monolithic applications...

Privilege Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft is the number one attack vector. Privileged...
Migrate and Modernize Cloud Applications Securely and Efficiently
As businesses prioritize their cloud strategies, interest in, as well as adoption of public cloud continues...

The Fastest Way to Modernize Apps Isn’t What You Think
When it comes to digital transformation, we hold these truths to be really, really evident: • Organizations...

Enterprise NoSQL For Dummies
NoSQL represents a fundamental change in the way people think about storing and accessing data, especially...

Sprinting Ahead With Agile Auditing
Internal auditors must be nimble to navigate today's complex business world, where they're expected to...
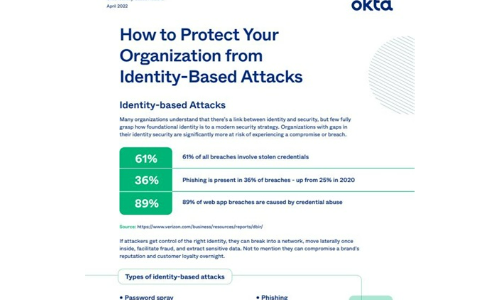
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Long-Term Data Retention with Veritas NetBackup
This white paper provides a technical overview of cloud storage as a long-term retention storage solution...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.