Compliance

Red Hat for cloud-native development
Application development is a complicated undertaking that requires a complex environment and tools. With...

IT and Cyber Incident Response Communication Templates
BlackBerry® Alert is a critical event management (CEM) solution designed to help organizations prepare...

For digital sovereignty and transparency in the cloud
Shared use of infrastructure not only saves resources but also enables companies to push ahead with digitalisation...
The Definitive Email Cybersecurity Strategy Guide
Email is your most essential business tool—and today's top malware delivery vector. This vital communications...

The Anatomy of an Insider Threat Investigation
For decades, perimeter-based security strategies have been the starting point for most cybersecurity...
Accelerate your journey to microservices-based applications with Citrix ADC
Today, new application architectures like Devops microservices are opening great opportunities for innovation....
2 Steps to Achieve Endpoint Compliance with KACE® by Quest
Next to ongoing security issues, meeting compliance mandates is one of the biggest challenges IT professionals...
Migrate and Modernize Cloud Applications Securely and Efficiently
As businesses prioritize their cloud strategies, interest in, as well as adoption of public cloud continues...

Building a Cloud-Native, Hybrid-Multicloud Infrastructure
Today's world is based on the hybrid cloud. Business interactions occur on-premises, through digital...
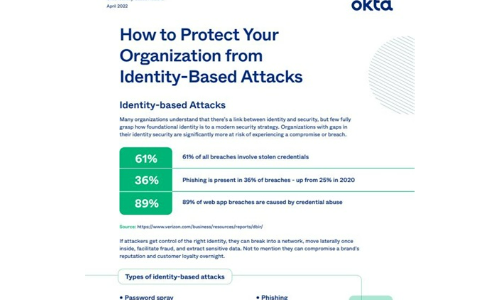
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...

Ransomware Threat Briefing
Cyber criminals are getting bolder and more sophisticated with their threats. No matter what kind of...

Zero Trust: The perfect solution for the perfect security storm
We're experiencing a classic example of the perfect storm. Never have organizations faced so many challenges...
State Of Cybersecurity Automation Adoption
Read this report to discover how CISOs and senior cybersecurity professionals are planning to accelerate...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
