Cloud Security

CISO’s Playbook to Cloud Security
To secure enterprise assets in the cloud, CISO's must address several new challenges unseen in traditional...

Achieving Operational Excellence in Food and Beverage Manufacturing
Sage Business Cloud Enterprise Management. The environment food and beverage manufacturers operate in...

Top 5 Challenges of Migrating Applications to the Cloud
As global workloads accelerate, the need for greater agility and global deployment options have driven...

Adaptive Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...

Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
Application Protection Report 2022: In Expectation of Exfiltration
Welcome to F5 Labs' Application Protection Report 2022. As in years past, the goal of this report is...

Keep your edge: Sage 200cloud buyer’s guide
Pressures dealing with increasingly complex operations, larger headcounts, and more customers developing...
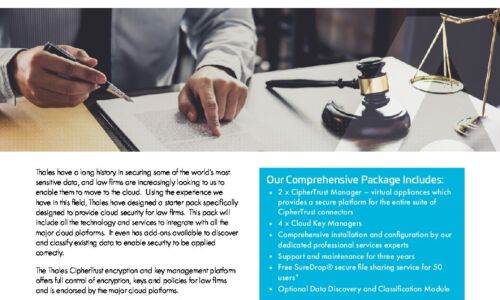
Complete Cloud Security for Legal Firms
Thales have a long history in securing some of the world's most sensitive data, and law firms are increasingly...

5 Things You Might Not Know About Cloud Security
Many organizations underestimate the security risks of the cloud, often assuming public cloud providers...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.