Authentication & Access Systems

Centralised Control Simplifies Management, Boosts Security
Aquila Heywood wanted to update its privileged access management processes to increase data security...

Filling the Gaps in Office 365
Office 365 offers a variety of choices and added functionality making it confusing for IT teams to decide...

Telstra's Best Practice Guide to Hybrid Cloud
Hybrid Cloud is becoming the strategy of choice for enterprises that want the best of both public cloud...

Modern SAP App Development with low-code
While digital transformation helps companies improve their ability to compete, it also poses a variety...
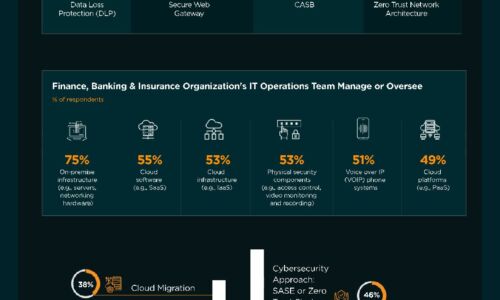
Finance, Banking & Insurance Industry | State of Cybersecurity 2021
This infographic by ISACA and HCL Technologies discusses the state of cybersecurity within the finance,...

The Case for Secure Communications
The tapping of voice communications has occurred virtually as long as electronic communication has been...

Veeam Enterprise Availability for SAP HANA
Enterprise-grade companies uses SAP HANA worldwide, this is the application directly related to customers...

Top 3 Challenges Your Team Faces When Building in the Cloud
Today's cloud and security teams are asked to do more with less. Although the capabilities and cost of...

Python for Data Science For Dummies, 2nd Edition
The fast and easy way to learn Python programming and statistics Python For Data Science For Dummies...
Transforming Security in the Mobile Cloud Era
In the age of digital transformation, maintaining secure interactions among users, applications, and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.